Ninety percent of incurred losses from cyber incidents targeting manufacturers over the past five years were ransomware-related. This, from a report by Resilience, underscores a brutal reality: ransomware isn’t just a nuisance for manufacturers; it’s an existential threat disguised as a financial transaction. Even more stark, ransomware comprised only 12% of Resilience’s total claim volume in that same period. That math screams specialization. Threat actors aren’t casting a wide, indiscriminate net; they’re targeting manufacturers specifically for fat paydays, and they’re succeeding far more often than not when they do strike.
This isn’t your uncle’s IT security problem anymore. The threat landscape has evolved. Ransomware groups have gone from smash-and-grab artists to meticulous planners, engaging in long-term campaigns and identifying high-value targets with alarming precision. For manufacturers, this is particularly problematic. Their business models often have a razor-thin tolerance for downtime. Every hour a production line is idled, revenue evaporates, supply chains fracture, and customer trust erodes. The opportunity for widespread damage isn’t theoretical; it’s baked into the very fabric of modern industrial operations.
The Numbers Don’t Lie: A Devastating Disparity
Let’s be blunt. The data from Resilience is eye-opening, and frankly, a little terrifying for anyone in the manufacturing sector. While ransomware might not be the most frequent type of cyber incident, its impact is disproportionately catastrophic. Imagine a scenario where 100 cyber incidents occur, but only 12 are ransomware. Yet, those 12 ransomware incidents are responsible for 90% of the total financial damage. It’s like having a few incredibly potent poison darts hitting your vital organs, versus a hundred mosquito bites. The latter is annoying, the former can kill you.
“Manufacturers don’t need to reinvent the wheel in the face of a growing threat. Our claims data, coupled with threat intelligence from the ROC, found that by auditing and validating MFA deployment, implementing procedural controls for financial transfers, investing in ransomware containment and response, and instituting other easy-to-implement practices can materially combat risk.”
This quote from Jud Dressler, Head of the Risk Operations Center at Resilience, is the glimmer of hope in an otherwise grim report. It’s not about deploying bleeding-edge AI defense systems or building impenetrable digital fortresses. It’s about fundamentals. Basic hygiene, applied rigorously.
Are Simple Adjustments Enough to Guard the Factory Floor?
Resilience’s report posits that manufacturers don’t need a complete technological overhaul. Instead, it’s about shoring up the perimeter and reinforcing internal processes. The six recommended steps are practical, achievable, and frankly, should be table stakes for any business of significant size and complexity, let alone one as critical to the global economy as manufacturing:
- Audit and validate Multi-Factor Authentication (MFA) deployment: This is the digital equivalent of a double-lock on your most valuable asset. MFA adds a critical layer of security that can thwart many credential-based attacks. The key here isn’t just having MFA, but ensuring it’s deployed everywhere it needs to be and working correctly.
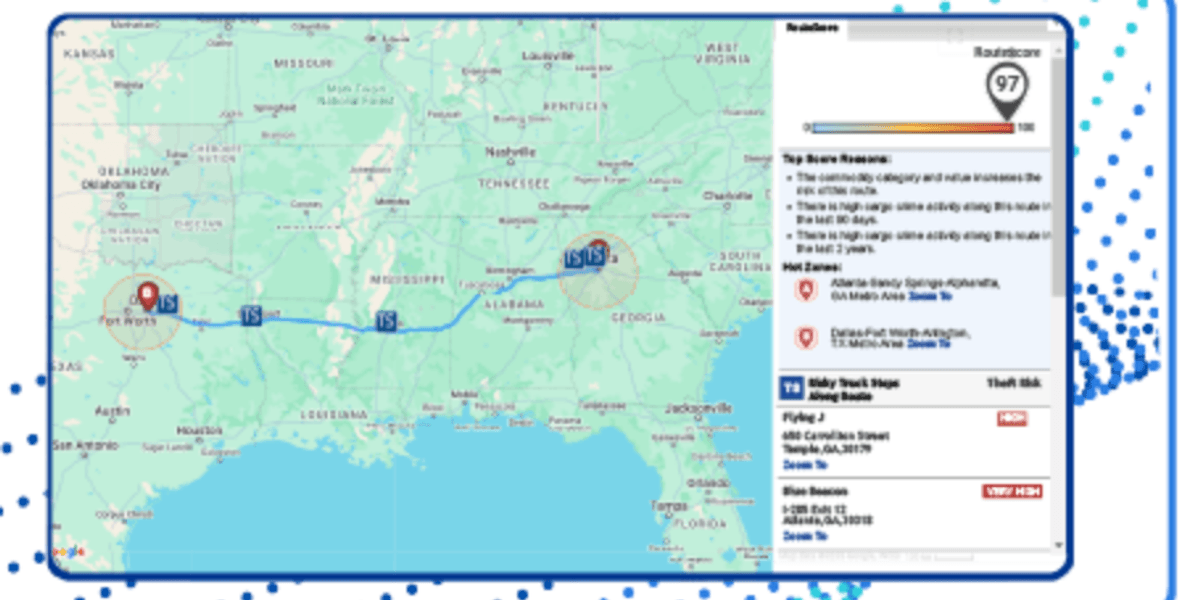
- Strengthen vulnerability management for external-facing systems: If your systems are exposed to the internet, they are a potential entry point. Regularly scanning, patching, and securing these vulnerabilities is akin to patching holes in your ship’s hull before it hits rough seas.
- Implement procedural controls for financial transfers: This addresses a common tactic where attackers compromise an executive’s email and trick finance into wiring funds. Clear, multi-person verification for significant financial transactions can prevent a devastating cash drain.
- Invest in ransomware containment and response: Accidents happen. Systems can get compromised. Having a well-rehearsed plan to quickly isolate infected systems and restore operations is crucial to limiting the blast radius.
- Extend security requirements to vendors and supply chain partners: Your security posture is only as strong as your weakest link. If your suppliers have lax security, they can become a backdoor into your own systems.
- Cyber risk quantification and transfer: Understanding your potential financial exposure and having appropriate insurance coverage is the final safety net. It’s about acknowledging the risk and preparing for the worst, even while actively working to prevent it.
Look, the sophistication of cyber threats, particularly ransomware, is escalating. While these suggested steps are indeed practical, the underlying threat intelligence suggests a more concerted and continuous effort is required. This isn’t a ‘set it and forget it’ situation. The hackers aren’t waiting around; they’re constantly innovating. Manufacturers need to view cybersecurity not as a cost center, but as an integral component of operational resilience, as vital as maintaining their machinery.
So, while the report correctly identifies that the wheel doesn’t need reinventing, it does need a fresh coat of paint, regular lubrication, and a vigilant driver. The era of treating cybersecurity as an afterthought is over for manufacturers. The data makes that abundantly clear.
🧬 Related Insights
- Read more: Last-Mile Delivery Optimization: Strategies to Reduce Costs and Improve Speed
- Read more: Gap Taps AI for Supplier Smarts [Traceability Boost]
Frequently Asked Questions
What is the main cyber threat for manufacturers?
The primary cyber threat for manufacturers is ransomware, which causes the vast majority of financial losses and operational disruption despite not being the most frequent attack vector.
How much do ransomware attacks cost manufacturers?
Ransomware attacks can lead to significant financial losses. Over the last five years, 90% of Resilience’s incurred losses from cyber incidents targeting manufacturers were attributed to ransomware.
What are the most important steps manufacturers can take to improve cybersecurity?
Key steps include auditing MFA, strengthening external system security, implementing financial transfer controls, investing in ransomware response, extending requirements to vendors, and quantifying/transferring cyber risk.