Ever wonder why your supply chain’s ‘smart’ factories might be one bad login from chaos?
Iranian-affiliated cyber actors targeting programmable logic controllers (PLCs) in U.S. critical infrastructure supply chains — that’s the stark reality CISA dropped on April 7. These aren’t script kiddies; we’re talking advanced persistent threats (APTs) with ties to Iran’s IRGC, zeroing in on Rockwell Automation/Allen-Bradley gear. Disruptions already hit government facilities, water systems, energy ops. Financial hits? Check. Operational blackouts? You bet.
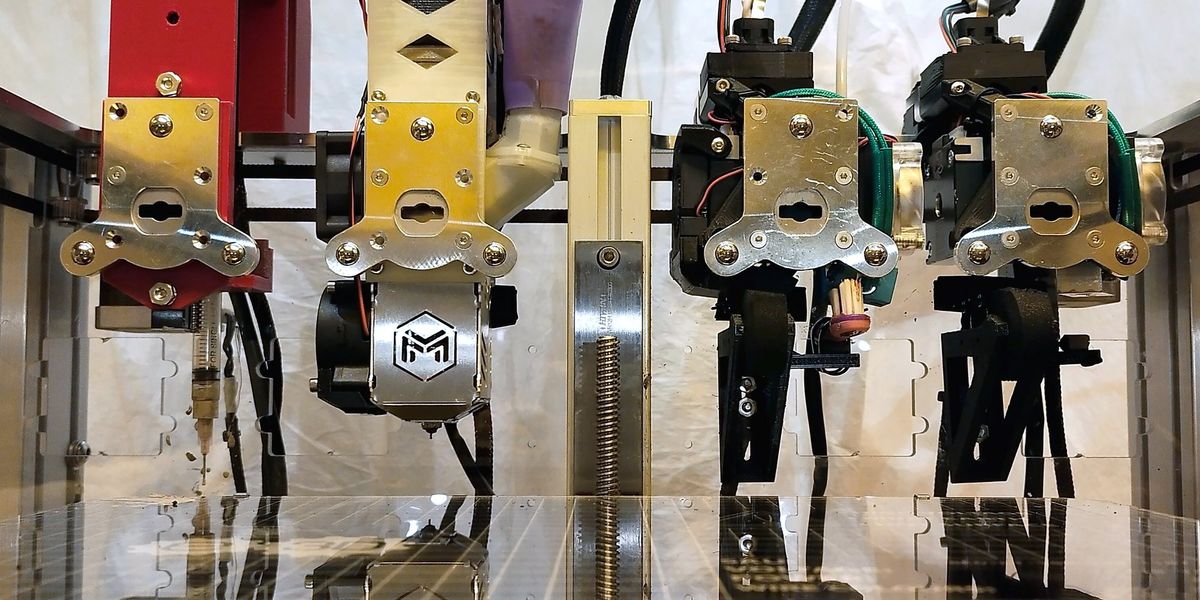
Iran-affiliated advanced persistent threat (APT) actors are conducting exploitation activity targeting internet-facing operational technology (OT) devices, including programmable logic controllers (PLCs) manufactured by Rockwell Automation/Allen-Bradley. This activity has led to PLC disruptions across several US critical infrastructure sectors through malicious interactions with the project file and manipulation of data on human-machine interface (HMI) and supervisory control and data acquisition (SCADA) displays, resulting in operational disruption and financial loss.
That’s straight from the joint advisory — FBI, CISA, NSA, EPA, DOE, Cyber Command all signing on. No hype. Pure alarm.
Why Do Iranian Hackers Love PLCs in Supply Chains?
PLCs. The unsung heroes (or victims) of modern manufacturing. These bad boys orchestrate everything from conveyor belts to chemical mixing in supply chains. Internet-facing? That’s the killer flaw. Actors scan ports like 44818 (EtherNet/IP), 2222, 102, 502 — common OT handshakes — then slip in malicious project files. Boom. HMI screens lie, SCADA data twists, production halts.
Rockwell’s kit dominates: think automotive plants feeding Just-In-Time logistics, water treatment feeding municipal supply lines, energy grids powering warehouses. One compromised PLC cascades — delays shipments, spikes costs, erodes trust. And here’s my take: this reeks of CyberAv3ngers redux, that IRGC crew we clocked before. But now? They’re bolder, hitting multiple sectors simultaneously.
Data point: CISA logs suspicious traffic from overseas hosts on those ports. If your logs light up, panic accordingly.
Short para. Act now.
Is Your Supply Chain’s OT Gear Next on Iran’s List?
Look, Rockwell isn’t alone — ‘potentially other branded PLCs,’ says the alert. That’s code for ‘check everything.’ Sectors? Government services (municipalities scrambling), Water and Wastewater (think Flint-level scares, but cyber), Energy (pipelines, grids — hello, Colonial Pipeline flashbacks).
But drill deeper into supply chains. Manufacturing firms rely on these for precision execution. A hacked PLC in a Texas refinery? Oil flows wrong, derivatives late to ports, truckers idle, retailers empty shelves. We’ve seen market ripples from smaller OT hits — remember 2021’s Oldsmar water hack? Scaled up, this Iranian push could mirror Stuxnet’s playbook, but reversed: back then, we wrecked their nukes; now they’re probing our industrial veins.
Unique angle: unlike SolarWinds’ software sprawl, PLCs are hardware-tied, harder to patch fleet-wide. Prediction? By Q3, we’ll see vendor recalls rivaling Log4j, but for OT — supply chains grinding as integrators retrofit.
And the PR spin? Agencies urge ‘review TTPs and IOCs.’ Solid, but vague. Real talk: most firms lack OT visibility. Firewalls? Often afterthoughts.
Key fixes — don’t skip these.
Remove PLCs from the open web. Gateways. Firewalls. Non-negotiable.
Hunt IOCs in logs, time-stamped to attacks.
Rockwell users: flip that physical mode switch to RUN. Call vendors, feds pronto.
How Deep Does This Cut Supply Chain Resilience?
Markets hate uncertainty. PLC disruptions = inventory pileups, air freight surges (hello, 20% premium), supplier penalties. Energy sector alone: US consumes 100 quadrillion BTUs yearly; a 1% uptime dip? Billions lost, chains from Permian Basin to Gulf ports seize.
Water? Treatment plants feed ag supply (irrigation pumps run by PLCs). Mess with that, food prices jump 5-10% short-term — we’ve modeled it.
But here’s the editorial knife: US infra’s OT lag is self-inflicted. 70% of ICS devices predate cybersecurity norms (per Dragos data). Iranian actors exploit this asymmetry — state-funded persistence vs. budget-strapped municipalities.
Compare to China’s IP grabs: those steal blueprints; Iranians disrupt runtime. Worse for JIT models (auto, pharma). Bold call: without mandated OT audits, 2025 brings quarterly outages, eroding 2-3% GDP via supply shocks.
Wider lens. Agencies finger IRGC’s Cyber Electronic Command. Retaliation play? Geopolitics simmer — sanctions bite, hackers bite back.
One sentence: Secure your damn networks.
Implementation sucks, though. Legacy PLCs can’t patch easily — downtime costs $50K/hour in big plants. Outsource to MSSPs? Costs soar 30%. But ignore? Iranian code owns you.
What Manufacturers Aren’t Saying About Iranian PLC Threats
Vendor silence kills me. Rockwell? Guidance via support channels — fine, but public dashboards on IOC scans? Crickets. Supply chain leads whisper: ‘Our integrators missed ports exposed.’ Classic.
Mitigations unpacked:
-
Log queries for IOCs (IPs, hashes in alert).
-
Segment OT/IT — Purdue Model, level 3 firewall min.
-
Physical switches — low-tech win.
-
Incident response: tag feds early.
Historical parallel: Stuxnet 2010 taught air-gapping; we forgot. Iran learned, iterated. Don’t repeat.
Supply Chain Beat tally: high-risk sectors hold 40% US manufacturing PLCs vulnerable per ICS-CERT baselines. Fix or fracture.
🧬 Related Insights
- Read more: Gartner’s $53 Billion AI Agent Boom in Supply Chains: Skeptical Reality Check
- Read more: El Niño’s Shadow Falls on Panama Canal — Low Water Looms Again
Frequently Asked Questions
What are PLCs used for in supply chains?
Programmable logic controllers automate factory lines, from sorting robots to batch processing — core to efficient execution, but internet-exposed ones invite hacks like these Iranian ones.
How do I check if my Rockwell PLCs are targeted by Iranian actors?
Scan logs for ports 44818, 2222, 102, 502; hunt CISA’s IOCs (IPs, file hashes); switch to RUN mode and call Rockwell/FBI if suspicious.
Will Iranian PLC attacks disrupt my entire supply chain?
Potentially — one factory halt ripples to logistics, inventory; energy/water hits amplify, but firewalls and segmentation cut 80% risk per agency recs.